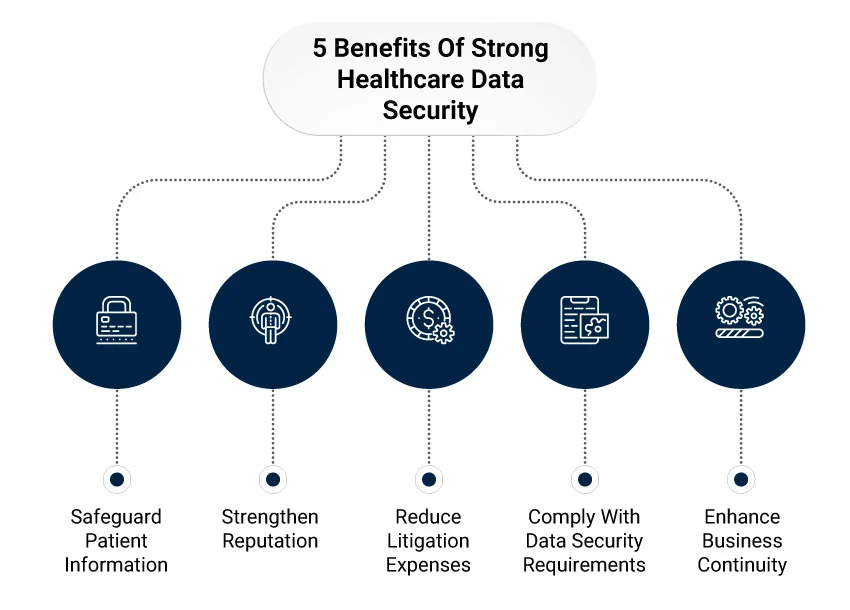
The Critical Importance of Healthcare Data Security
Healthcare organizations hold some of the most sensitive information imaginable—medical histories, diagnoses, treatment plans, genetic data, and financial information. This data is not only deeply personal but also highly valuable to cybercriminals, making healthcare a prime target for data breaches and ransomware attacks. The consequences of inadequate security extend beyond financial penalties to include reputational damage, loss of patient trust, and potential harm to patient care.
The Health Insurance Portability and Accountability Act (HIPAA) establishes national standards for protecting patient health information. Compliance is not optional—violations can result in penalties ranging from $100 to $50,000 per violation, with annual maximums reaching $1.5 million per violation category. Beyond legal requirements, ethical obligations to protect patient privacy demand robust security practices.
Understanding HIPAA Requirements
HIPAA comprises several rules that collectively define how protected health information (PHI) must be handled, secured, and disclosed. Understanding these requirements is the foundation of compliance.
The Privacy Rule
The Privacy Rule establishes national standards for protecting PHI, defining what constitutes PHI, who can access it, and under what circumstances it can be disclosed. It grants patients rights to access their own health information, request corrections, and receive accounting of disclosures.
Organizations must implement policies and procedures that limit PHI access to the minimum necessary for each purpose. Not everyone in your organization needs access to all patient data—implement role-based access controls that restrict access based on job function.
The Security Rule
The Security Rule specifically addresses electronic PHI (ePHI), requiring covered entities to implement administrative, physical, and technical safeguards. Unlike the Privacy Rule, which applies to all forms of PHI, the Security Rule focuses on electronic data and the systems that store, process, and transmit it.
The Security Rule is flexible, recognizing that different organizations have different needs and resources. It specifies required outcomes rather than prescribing specific technologies, allowing organizations to implement appropriate security measures based on their size, complexity, and risk profile.
The Breach Notification Rule
When breaches occur, the Breach Notification Rule requires covered entities to notify affected individuals, the Department of Health and Human Services, and in some cases, the media. Notification must occur within 60 days of breach discovery. This requirement emphasizes the importance of breach detection capabilities and incident response procedures.
Administrative Safeguards
Administrative safeguards are policies and procedures that govern how an organization manages the security of ePHI. These form the foundation of your security program.
Risk Assessment
Conduct regular, comprehensive risk assessments to identify threats and vulnerabilities to ePHI. Assess the likelihood and impact of potential security incidents, and implement measures to reduce risks to reasonable and appropriate levels. Risk assessment is not a one-time activity—it should be ongoing, especially when implementing new systems or making significant changes to existing ones.
Security Management Process
Establish policies and procedures to prevent, detect, contain, and correct security violations. This includes incident response procedures that define how to identify, respond to, and recover from security incidents. Document these procedures and train staff on their roles and responsibilities.
Workforce Security
Implement procedures for authorizing, supervising, and terminating workforce access to ePHI. Conduct background checks appropriate to the level of access being granted. Provide security awareness training to all workforce members, ensuring they understand their responsibilities for protecting patient information.
When employees leave or change roles, promptly revoke or modify their access to ePHI. Terminated accounts represent a significant security risk if not disabled immediately.
Business Associate Agreements
Third parties that handle PHI on your behalf—cloud providers, billing services, IT contractors—are business associates under HIPAA. You must have written agreements with all business associates that specify their responsibilities for protecting PHI and their liability in case of breaches.
Don't assume that business associates are compliant simply because they claim to be. Verify their security practices, review their compliance documentation, and include audit rights in your agreements.
Physical Safeguards
Physical safeguards protect the physical systems, buildings, and equipment where ePHI is stored and accessed.
Facility Access Controls
Limit physical access to facilities containing ePHI to authorized personnel. Implement badge systems, visitor logs, and surveillance cameras. Ensure that areas containing servers or workstations with ePHI access are secured when unattended.
Workstation Security
Implement policies governing the use of workstations that access ePHI. Position screens to prevent unauthorized viewing. Enable automatic screen locks that activate after short periods of inactivity. Prohibit leaving workstations logged in when unattended.
Device and Media Controls
Establish procedures for the disposal and reuse of devices and media containing ePHI. Simply deleting files is insufficient—use secure wiping tools that make data unrecoverable. For devices being disposed of or repurposed, physically destroy storage media or use certified data destruction services.
Maintain inventories of all devices that store or access ePHI. This inventory enables you to track devices, ensure they're properly secured, and account for them during audits.
Technical Safeguards
Technical safeguards are the technology and policies that protect ePHI and control access to it.
Access Controls
Implement unique user identification for everyone who accesses ePHI—no shared accounts. Use strong authentication mechanisms, including multi-factor authentication for remote access and privileged accounts. Automatically log users off after predetermined periods of inactivity.
Implement role-based access controls that grant access based on job function. Regularly review access permissions to ensure they remain appropriate as roles change.
Audit Controls
Implement systems that record and examine activity in systems containing ePHI. Log who accessed what information, when, and what actions they performed. Regularly review these logs to detect unauthorized access or suspicious activity.
Retain audit logs for sufficient periods to support investigations and compliance demonstrations. Protect logs from tampering by storing them in secure, append-only systems.
Integrity Controls
Implement mechanisms to ensure that ePHI is not improperly altered or destroyed. Use checksums or digital signatures to detect unauthorized modifications. Maintain regular backups that enable restoration of data if integrity is compromised.
Transmission Security
Protect ePHI transmitted over electronic networks from unauthorized access. Use encryption for all transmissions over public networks, including email, web access, and file transfers. Implement virtual private networks (VPNs) for remote access to systems containing ePHI.
Don't overlook internal network security. Segment networks to isolate systems containing ePHI from general corporate networks. This limits the impact of breaches in less-sensitive systems.
Encryption Best Practices
While HIPAA does not explicitly require encryption, it is "addressable," meaning organizations must implement it or document why an alternative measure is equivalent. In practice, encryption is essential for protecting ePHI.
Encryption at Rest
Encrypt all storage containing ePHI—databases, file systems, backups, and portable devices. Modern operating systems and database platforms provide built-in encryption capabilities. Enable these features and manage encryption keys securely, separate from the encrypted data.
Encryption in Transit
Use TLS/SSL for all web traffic involving ePHI. Configure email systems to use encryption for messages containing patient information. For file transfers, use secure protocols like SFTP or HTTPS rather than unencrypted FTP or HTTP.
Incident Response and Breach Management
Despite best efforts, security incidents will occur. How you respond determines the impact on your organization and patients.
Incident Response Plan
Develop and document an incident response plan that defines roles, responsibilities, and procedures for responding to security incidents. Include procedures for containment, investigation, remediation, and notification. Test the plan regularly through tabletop exercises and simulations.
Breach Assessment
When potential breaches occur, conduct rapid assessment to determine whether notification is required. HIPAA requires notification only for breaches affecting more than a low probability of compromise. Document your assessment process and conclusions.
Notification Procedures
If breach notification is required, act quickly. Notify affected individuals within 60 days, providing information about what happened, what information was involved, what you're doing to address the breach, and what individuals can do to protect themselves. Notify HHS and, for large breaches, the media.
Ongoing Compliance
HIPAA compliance is not a one-time achievement but an ongoing process requiring continuous attention and improvement.
Regular Audits
Conduct regular internal audits to verify that security controls are functioning as intended and policies are being followed. Address identified gaps promptly. Consider engaging third-party auditors periodically for independent assessment.
Policy Updates
Review and update policies and procedures regularly to address new threats, technologies, and regulatory guidance. Ensure that updates are communicated to affected workforce members and that training is provided on significant changes.
Training and Awareness
Provide security awareness training to all workforce members at hire and annually thereafter. Training should cover HIPAA requirements, organizational policies, common threats like phishing, and how to report security incidents. Make training engaging and relevant to employees' roles.
Conclusion
Protecting patient health information is both a legal requirement and an ethical imperative. HIPAA provides a framework for security, but compliance requires ongoing commitment, investment, and vigilance. Organizations that prioritize security, implement comprehensive safeguards, and foster a culture of privacy protection not only meet regulatory requirements but also build patient trust and protect themselves from the devastating consequences of data breaches.